VPN or Virtual Private Network started as a service to facilitate secure access to private networks over the internet (or public connection). At the time, the primary use-case scenario for the service was to create a secure channel to access information within governments, organizations, and businesses, without inflicting a threat to their data. However, over the years, as products and services leveraging the personal information of users started taking center stage on the internet, the need for secure and private access prompted the demand for something as sophisticated and secure as VPN to come into the mainstream for personal use.
Even today, as its adoption for personal use continues to grow among the masses, and the service appears to be one of the promising and secure solutions to access information while preserving user identity, it is still not the safest bet and has its share of flaws and shortcomings, which implies that even VPNs aren’t perfect, after all.

To fathom this narrative, it is imperative to understand the working of a Virtual Private Network and its underlying intricacies that may lead to potential vulnerabilities and hold the scope of identity leak. So, let’s begin by first answering the most obvious questions and slowly delve into the concerns that follow.
What is a VPN and what purpose does it serve?
A VPN (or Virtual Private Network) is a modern-day solution comprising of various protocols that allow users to access information over the internet in a secure and anonymous (sort of) manner.
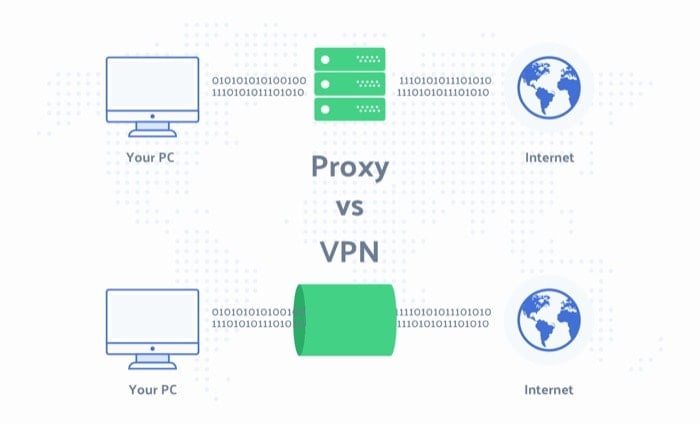
Or, in general, you can also refer to it as a glorified proxy. As in most cases, the basic idea behind both a VPN and a proxy is essentially the same — to act as a middleman between your device and the server (you are connecting to) — in a way that allows you to disguise the source of the request and maintain anonymity. However, while the two share a similar working principle, it is worth noting that, unlike proxy servers, VPNs come with additional features and security measures — that is, when granted, the VPN provider abides by the claims and policies it suggests to practice.
Talking about applications, compared to the initial days of its inception, the modern VPN service extends the scope of application even further. From offering an encrypted channel to access public WiFi — to providing secure access to a private network — to something as basic as bypassing geographic restrictions to view geo-blocked content across OTT platforms — among others. However, despite the range of applications it offers to assist in different scenarios, it is the way in which it performs these operations, which raises several questions.
How does a VPN work?
Moving right along, before delving straight into the concerns associated with a VPN, we must look at a brief overview of its working principle to better understand the potential for some of the underlying vulnerabilities. As mentioned a couple of paragraphs earlier, you can think of VPNs as glorified proxies. Since, to a greater extent, they offer the same basic functionality. So when you use a VPN, in essence, you are leveraging a proxy to make requests on your behalf to the destination server. And by doing so, you are, in turn, eliminating the need to establish the connection yourself, which, in a way, helps you stay anonymous on the internet to some degree.
To understand this, consider an example where you try to visit a geo-restricted website in your region. While you do that, the server can identify the source of request using the IP address provided by your ISP. And, in turn, can prevent you from establishing a connection and accessing its services. However, when you introduce VPN into the picture, the situation changes altogether. As now, when you use a VPN client to request access to the restricted website, the server notices the request to be originating from the same region it is being hosted. Thus, permitting you access to its services. Moreover, since the channel between your device and the ISP is encrypted, it prevents your ISP from identifying the request and the response on either end of the connection. As a result, you eventually manage to bypass the restriction despite being located in some other part of the world.

Similarly, when you use a VPN with the idea to browse the internet securely and anonymously, the service creates an encrypted tunnel between your device and the ISP and uses tunneling to prevent your ISP from viewing your online activity. Moreover, it also masks your IP (Internet Protocol) address with some random address, which ensures you stay anonymous while surfing the internet. However, that is not to say an IP address is completely untraceable, as there are certain loopholes with VPNs that can be exploited to recover such information.
What are the problems associated with a VPN? And why they aren’t perfect?
When you use a VPN client on your device, even though the connection is encrypted and your IP is masked, you can still be tracked using other parameters. As it turns out, an IP address is a small piece of trackable information in your internet profile. And there are other unique clues for your internet identity that can help an attacker or advertiser generate your internet profile. Not to mention, in some cases, the VPN service provider could itself be susceptible to attacks. And as a result, it might get compromised and leave you vulnerable with all your information ending up on the internet.
1. Vague Privacy Policy
While most VPN providers do suggest that they follow strong encryption standards to secure your data on the internet and that they do not track your online activity to ensure your privacy is never compromised, it seems dubious with a majority of the service providers, especially the ones that offer their services for free. This, in itself, is a big concern. As what most of these services mention in their privacy policy is not something they strictly abide by. And oftentimes, there is either some vague element in the policy or a completely missing clause altogether, that is far fetched for an average user to find out instantaneously at the time of sign up. Moreover, a lot of the features and security measures these services suggest offering is filled with a slew of tech-jargon — to an extent where it is quite overwhelming for an average user, and gives them a false sense of hope about the services’ privacy measures, to promptly get them onboard.
2. Hiding your IP is a must
In the same vein, a large number of VPN providers also seem to create a state of urgency or panic among users, suggesting that an IP address holds the key to a lot of their personal information. And therefore, one must sign up for their VPN service to mitigate this concern, and in turn, improve their privacy. Although, at large, this is not completely wrong, as an IP address does hold the key to some of the crucial profiling elements of a user on the internet. But, that does not, however, suggest that an IP address is the single most entity that holds the key to more personal data about a user, as there are various other factors too, which can help someone track a user on the internet. Thus, suggesting that the claims from these VPN providers are nothing but solely marketing affirmations.
3. Logging and selling user information
Taking it further, the other major concerns with VPNs that linger on the surface, but mostly get unnoticed, are logging and selling of user information. If you use a free VPN client, your online activity is likely to be logged by the service and stored on its servers. The recorded logs generally include information such as your IP address, the sites you visit, timestamps for connection/disconnection, data transfer during sessions, and more. However, there aren’t many services that put it outright that they do not log any user information. Instead, what these services rather do is use ambiguous messages in their policies to make things all the way more confusing for users to comprehend and make an informed decision. Although there are a few exceptions — most likely the paid services — that do stand up to their claim of no-logging of user information. But sadly, they too refrain from explicitly mentioning “no logging” in their privacy policy. To add to that, in the past, some of the popular services have been found guilty of logging user data without them knowing.
4. Marketing DNS leak prevention as a feature
Besides no-logging claims, VPN service providers also claim to prevent DNS-leakage, which is a term used to refer to a situation where the service fails to tunnel your DNS requests, and instead, it ends up with your ISP. To give you a quick primer, a DNS or Domain Name System is a decentralized server that is responsible for holding records of domain names and their associated IP addresses. So, for example, when you enter youtube [dot] com, the DNS comes into play to resolve the domain name with its designated IP address to present you with the result for your query. Coming back to DNS leak, what this essentially means is that, in an ideal scenario, when you request a website over a VPN, it should get resolved instantaneously, and you must have the page open on your device. However, in certain instances, the VPN fails to keep this a secret and ends up leaking the DNS entry for your requested website with your ISP. And even though some services suggest offering it as a feature, the idea seems kind of pointless in the first place, since ensuring DNS leaks don’t happen while you use a VPN, should be a rudimentary functionality, and not something that the service providers need to market as a feature.
5. Traffic encryption promises
Last, but certainly not the least, is the concern over encryption, which seems to create a lot of confusion among users. While most service providers claim that using a VPN encrypts your data with strong encryption standards before it ends up on the public network, the wordplay here is something that causes the user to fall for their promises and subscribe to the service right away. As, even though the data is encrypted by the service, it is the degree to which it is encrypted that plays a crucial role. What this essentially means is that the part of the communication that is encrypted determines the level of privacy and data security one can expect out of the service. In most cases, the VPN providers encrypt the part of the communication that involves the connection between your device and ISP, leaving the transmission of data from the ISP to the destination server unencrypted. So, while the data flows through the secure tunnel between your device and the ISP, you can be assured that it is secure from the prying eyes. However, what happens beyond the ISP through to the destination server, is all unencrypted, leaving it in pretty much the same situation as it would be with no VPN in the first place.
All these concerns leave the end consumer in uncharted territory, where, in a majority of cases, despite paying for a premium, the users are still not convinced whether the service offers complete anonymity and does not put their information at risk. Moreover, the policies on some of the services do not clearly describe how they handle user’s data and what measures they take to deal with targeted advertising.
Should you use a VPN at all?
After discussing various elements that can play a part in leaking your personal information and render your VPN service useless, there are certain use-case scenarios in which the service can actually prove to be helpful. However, it is worth mentioning that, you must do thorough research on the shortlisted options and compare them with other services on your list. And most importantly, you MUST READ THEIR PRIVACY POLICY CAREFULLY before making a decision and spending your money on a subscription. Not to mention, you must strictly avoid falling for “free” VPN services, as almost all of these services sell your personal information to advertisers in exchange for money to generate revenue for the functioning of their services and could also be monitoring users’ traffic for foreign intelligence. This is a fairly overlooked aspect by most people who are just getting started with a VPN, and oftentimes, they fall for such free services. However, there are a few services that offer a free trial for users to check out the service themselves, before spending their money on its subscription, which goes on to suggest that, you can trust such services, granted you check their privacy policy thoroughly.
Although during the course of the article, we did emphasize on how VPNs have their disadvantages and drawbacks, and that, they aren’t perfect in any sense and should not be trusted blindly, we are in no way suggesting you to abandon them altogether. But rather, asking you to limit its usage to crucial situations only. For instance, you can use a VPN to access resources on a company’s private network, bypass geo-restricted content, circumvent ISP-level content blocking, or even to access public networks in hotels or cafes in urgent situations.
Besides, if you are open to considering some other alternatives to VPN, there are other working solutions for different use-case scenarios to help you alleviate the need for a VPN in the first place. Some of these alternatives include Smart DNS — to disguise your location to access geo-restricted websites; Tor (The Onion Router) — to increase your security and anonymity and to bypass restrictions; mobile applications such as Orbot and Orfox — that helps you redirect the traffic on your device through Tor; among other solutions.



