The DNS over HTTPS (DoH) protocol has gained a lot of traction lately, particularly from some of the top internet browsers and the companies advocating user privacy. It is claimed to be a way for users to improve their online privacy by sending their DNS requests (and responses) in an encrypted form. Thus, reducing the chances of being tracked and attacked by any third-party or ISP, on the internet. However, not everyone seems to be happy with the new protocol, and have reasonings to back their objection. But, given the advantages that DoH has to offer, it does not hurt to try out and check the protocol in action, yourself. So, if you happen to be interested, here’s a guide explaining what DNS over HTTPS is, what are some of its advantages, and how you can enable it across different internet browsers.
What is DNS over HTTPS (DoH)?
To understand the DNS over HTTPS (DoH) protocol, it is customary to, first, understand what DNS is and how your requests are sent across the internet. In layman terms, DNS or Domain Name System is a decentralized directory of all the different websites on the internet and their associated IP (Internet Protocol) addresses. It can be considered as a service that allows you to enter the domain name of a website (eg. google.com) instead of its IP address (say, 172.217.26.238) to make it easy and convenient for you to access different websites on the internet without having to remember their IP addresses — which would, otherwise, prove to be an arduous task.

When you make a request to access, say, google.com, your ISP (Internet Service Provider) receives it and sends a connection request to the server for the website you are connecting — Google, in this case — to get a suitable response. It is at this point that the DoH protocol comes into play. For, in a general scenario, the request made from your ISP to a website’s server is unencrypted, irrespective of whether the website uses HTTP (Hypertext Transfer Protocol) or HTTPS (Hypertext Transfer Protocol Secure) protocol. As a result, anyone in between you and the destination server can snoop on the network to collect personal information.

With the DNS over HTTPS (DoH) protocol in place, all the DNS traffic between you and the destination server is encrypted. By doing so, the protocol enables the transfer of DNS requests (and the associated response) over a secure and encrypted connection. Thus, preventing any third party, including your ISP, from tracking you and your online activity on the web.
What does DNS over HTTPS (DoH) offer, and how does it work?
As mentioned in the previous point, the DNS over HTTPS protocol enables an encrypted communication channel for DNS requests and responses, preventing those with prying eyes from eavesdropping on your online activity. By having an encrypted communication channel, the protocol ensures that no one in between can snoop on the DNS packets as they are sent and received. However, that is not to say that the protocol completely eliminates any scope of intrusion or tracking. As, the HTTPS protocol (and even DNS, for that matter) have their share of drawbacks and disadvantages that can be exploited in some ways to gain access to the communication between a user’s computer and the server of the website they are connected/trying to establish the connection with.

But, like any other preventive measures you take to keep your online data private and secure and maintain some sort of anonymity on the web, it does not hurt to have an extra layer of security to keep your online activities secure. And with DNS over HTTPS, that is precisely what we are trying to do — get a more secure hold over our online communication by securing the DNS packets as they are transmitted and received.

Moving to its working, the DNS over HTTPS protocol requires two things to work in tandem to be effective: A doH-supported DNS server and a DoH-compatible app/service. Essentially, when an app/service that supports the DoH protocol makes a request to a website’s server, it is sent across as an HTTPS request to the DoH server (or resolve), where the resolver processes the request and reverts with a response back to the app/service — all via an encrypted channel. The encrypted channel here ensures (or makes it difficult) anyone snooping on your network (including the ISP) can not view your requests, track activities, and alter the responses to masquerade as the website (you are trying to access) to attack and dupe you to into collecting your personal data/information.
Also Read: 7 Best DNS for Gaming
How to enable DNS over HTTPS (DoH)?
DNS over HTTPS was first introduced by Mozilla on its Firefox browser. It is still the only browser out there that offers the feature built-in and, in some cases, has it enabled by default. Moreover, it also gives the option to select the desired DNS provider from the list of a bunch of DNS providers. On the other hand, some of the other popular browsers, especially those based on Chromium, do not offer the functionality built-in to the browser, like Firefox. However, there is a way to get the protocol up and running on these browsers as well. So, depending on the browser you use, follow the steps listed below to enable DoH on your browser.
Mozilla Firefox
If you live in the US, Mozilla automatically enables DNS over HTTPS in Firefox by default. However, if you are from some other part of the world, you can enable the same with the help of the following steps.
1. Open Firefox, hit the hamburger menu from the right-hand side, and select Preferences. Alternatively, hit the [command + ,] shortcut to go into Preferences directly.
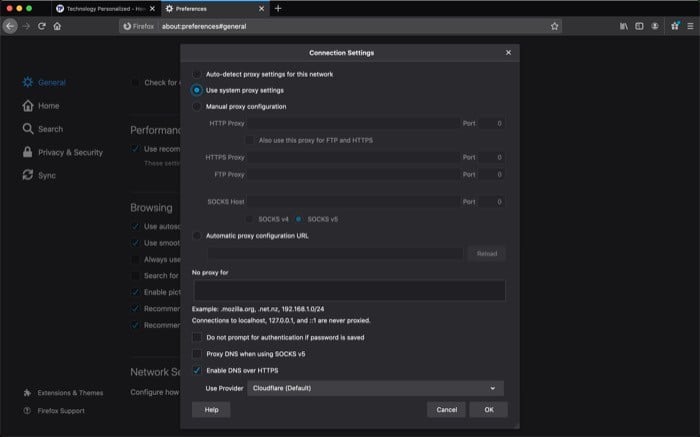
2. In the Preferences window, scroll down all the way to Network Settings, and from there, tap on the Settings button.
3. Now, in the Connection Settings pop-up, scroll down to the bottom and check the checkbox that says Enable DNS over HTTPS.
4. To change the provider, hit the dropdown menu next to Use Provider and select a provider from the list.
5. Finally, hit OK.
Brave/Google Chrome/Microsoft Edge
If you use Brave, Google Chrome, or Microsoft Edge, you would be aware that all of these browsers belong to Google’s free and open-source project, Chromium. As a reason, you can enable DNS over HTTPS on any of these browsers using the same procedure. Moreover, unlike Mozilla Firefox, Chromium as a platform does not provide an option to enable DoH right away. So, to have the protocol up and running on any of the Chromium-based browsers, you are required to leverage the power of flags. And since these browsers share the same Chromium codebase, enabling flags on all three involves the same steps.
For those unaware, Flags are experimental tweaks that allow users to add/improve the functionality of their browser. They are not a part of the browser’s official offerings, and nor are they explicitly available in the browser. Since Brave, Microsoft Edge, and Chrome are based on Chromium, they come with support for flags. To enable the DoH protocol, follow the steps mentioned below.
1. Open Brave/Google Chrome/Microsoft Edge.
2. Depending on what browser you are on, tap on the address bar and enter the command accordingly:
i. Brave – brave://flags/#dns-over-https
ii. Google Chrome – chrome://flags/#dns-over-https
iii. Microsoft Edge – edge://flags/#dns-over-https
3. Unlike Firefox, which provides a few options for DNS within the browser settings, if you use the other three browsers, you need to change the DNS from your machine’s settings for it to be able to work with DNS over HTTPS.
4. Restart the browser.
Besides the Chromium-based browsers, if you use Safari for browsing the web on your Mac, you are out of luck. As with the current version of its operating system, macOS Catalina, Apple does not provide support for the DoH protocol on Safari or any other app/service. Although, at this year’s WWDC, the company did mention its plans to bring support for DNS over HTTPS on its apps/services with the upcoming version of macOS, the Big Sur.
By now, you should have an understanding of what DNS over HTTPS is, how it adds to your privacy on the internet, and how to enable it across different internet browsers. Once in place, you can rest assured that you are now less susceptible to MITM (and DNS) attacks and can browse the web with a certain sense of peace in the mind since you are not subject to continuous tracking by advertisers across the web.